Case Studies & Expert Insights
Explore expert insights and case studies from Liverton Security.

Complexity of Security (Part 1)
All Case Studies & Expert Insights
Deep dive into solutions and cybersecurity topics with our experts

One of the biggest security risks in New Zealand isn’t technology. It’s misplaced responsibility
Many organisations assume cybersecurity is handled by their IT or network provider, but IT operations and security are not the same discipline. While firewalls, endpoint tools, and cloud controls are important, security fails when it becomes technology-led instead of risk-led. Real security requires governance, skilled people, and continual review—not just tools left to run on default settings. Without dedicated security leadership and maturity assessment, organisations can appear secure on paper while remaining exposed in practice.
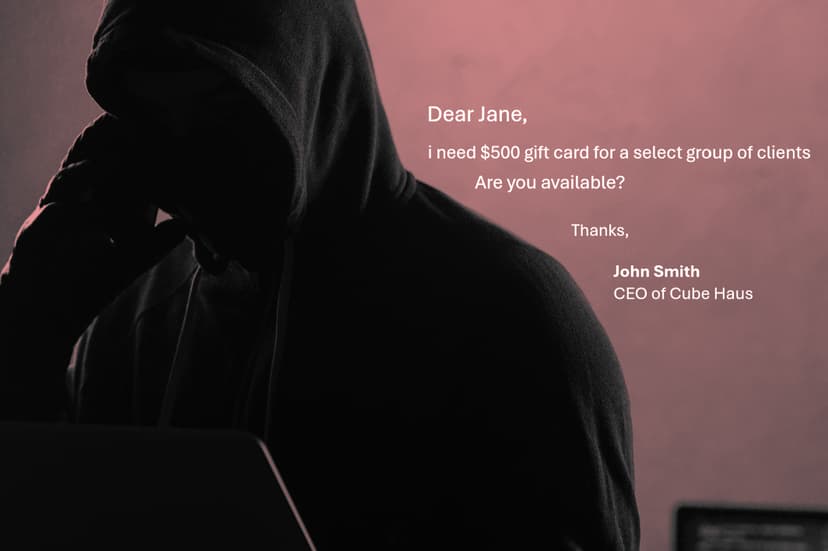
The $500 Gift Card That Nearly Cost Millions: Understanding Executive Email Spoofing
A seemingly harmless email request from the CEO asking a new employee to purchase gift cards led to a serious security incident. This real-world case study shows how preventable failures and weak email security controls can result in significant financial and reputational damage, underscoring the critical importance of robust email security in modern organisations.

Why New Zealand’s Health Application Ecosystem Needs Security Baselines, Not Just Privacy Law
Privacy law plays a vital role in protecting patient information, but it does not define how that data must be secured. In New Zealand’s growing ecosystem of health applications, the absence of mandatory security baselines creates systemic risk across patient portals, practice management systems, and third-party services. Recent events have highlighted why privacy compliance alone is no longer enough to protect sensitive health data.

Manage My Health Is Not an Outlier: Why Small Health Providers Are Being Targeted—and Why Email Is Still the Front Door
The Manage My Health data breach wasn’t just one of New Zealand’s biggest cybersecurity incidents — it exposed a pattern affecting small and mid-sized healthcare providers nationwide. As privacy obligations race ahead of enforceable security standards, the incident points to a systemic risk and raises uncomfortable questions about how health data is really being protected.

Complexity of Security (Part 2)
Complexity is a sign of sophistication in security. The more tools, the more policies, the more detailed the controls, the safer we must be, right? The truth is vastly different. Complexity is the enemy of security. When security systems are too complex, they create fear, confusion, and disengagement.

Complexity of Security (Part 1)
Security doesn’t fail because people don’t care—it fails when it’s too complex. With organisations juggling dozens of security tools, confusion has become a hidden vulnerability. Cybersecurity expert, Andrew Johnston, explains how over-engineered systems and technical language drive people to bypass security, and why simplicity—not more controls—is the key to building security that actually works.