The Governance Gap: Speed vs. Structure
By Andrew Johnston | 3 May 2026
Summary
Fast-moving organisations often prioritise speed over structure—but this creates a hidden governance gap. When security, risk, and accountability are not built into the foundation, businesses expose themselves to serious operational and regulatory consequences. This article explores where governance commonly breaks down and outlines practical steps to embed it as a core business function.
Emerging organisations, such as those in the tech sector are fundamentally designed for rapid iteration. This "Move Fast and Break Things" or “Break Fast and Fix Fast” agile based models that have contributed to the creation of an ethos that treats security and compliance as overhead, rather than an embedded, foundational component of the product and the business model itself.
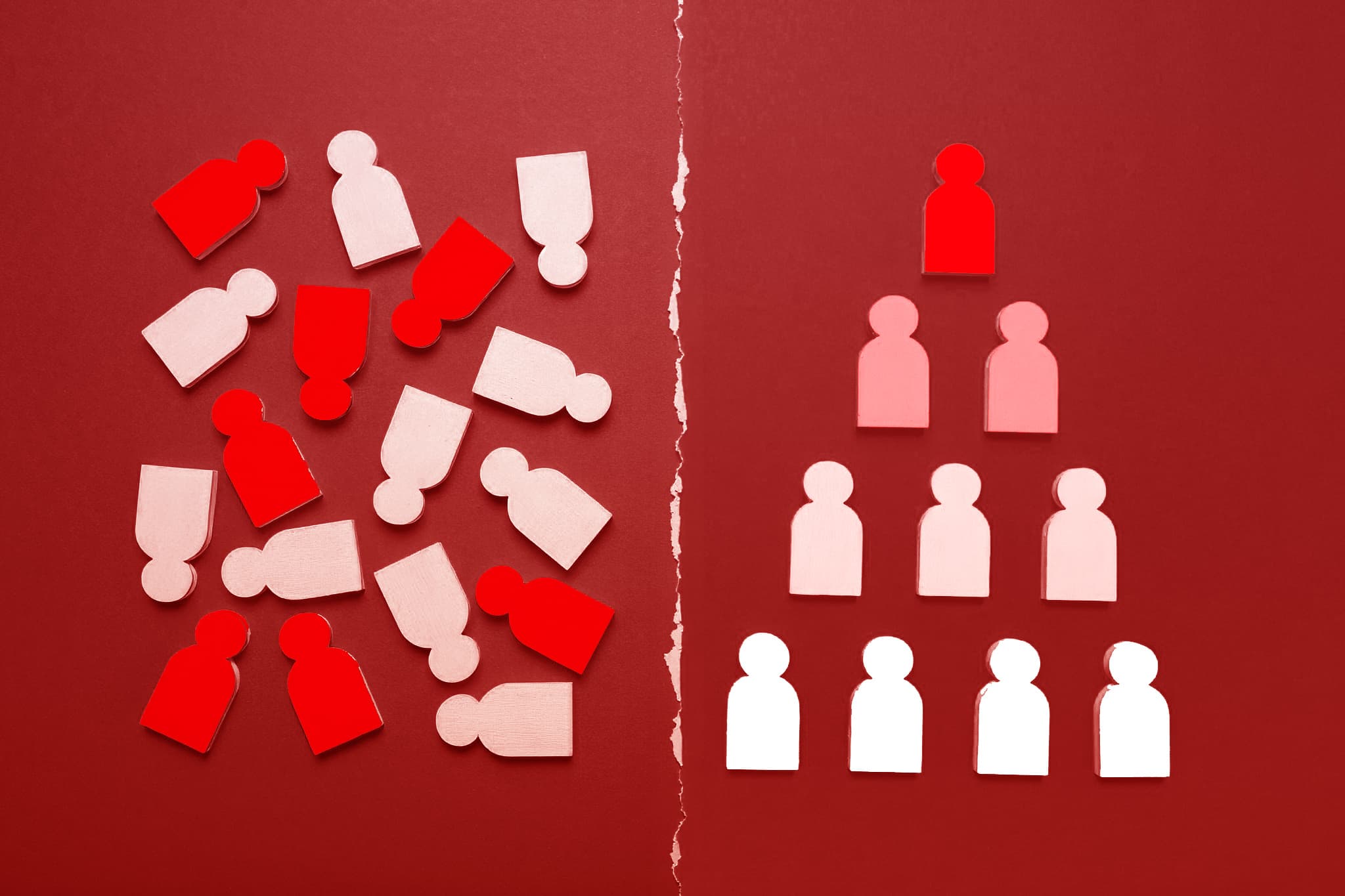
Ultimately the buck stops with the Board who are responsible for the governance of risk including the risk imposed by cyber security failures. The resulting governance vacuum manifests in three key areas:
1. The Design Phase Failure
The Design Phase Failure (Security by Design) Governance should be a process that runs parallel to product development, not a roadblock applied at the end. When security is an afterthought, the foundational architecture is compromised. This leads to:
Blind Spots in Data Flow: Data is moved, stored, and processed across various microservices without a clear, documented data flow map. No one knows where sensitive data actually lands, for how long is it protected and how.
No Initial Data Classification: The organisation is handling Personal Identifiable Information (PII) and sensitive business data without formally classifying it (e.g., Public, Internal, Confidential, Restricted). Without classification, you cannot enforce proportionate security controls.
2. The Operational Failure (Control Maturity)
Most emerging companies treat their infrastructure as a series of interconnected cloud services (AWS, Azure, etc.) and believe that paying for the service provider constitutes governance. Just because the organisation is using a commercial cloud service you cannot escape the fundamentals “It Does Not”. This results in:
Poor Vendor Risk Management (VRM): The company relies on a patchwork of APIs and third-party services without adequately vetting their security posture or understanding their data handling requirements.
Manual Processes: Key operational procedures (onboarding, access revocation, patch management) are performed manually and inconsistently, creating human error and audit failures.
3. The People & Policy Failure (Accountability):
The governance structure often lacks clear ownership. Everyone knows security is important, but no single individual or small committee owns the governance framework itself.
Lack of Policy Depth: Policies exist e.g., "We must protect customer data", but they lack the necessary detail i.e. who is accountable for the protection, what the acceptable risk level is, and how often must that process be audited.
Lack of Risk Definition: Organisations that accept risks without understanding them and recording them in a formal manner will lose track of what data and information they have, and people accept risks who are not authorised to for expedience which takes us back to point 1.
Remediation: Where to Focus Governance Efforts

To close this gap, an organisation needs to move beyond simple compliance checklists and implement a genuine governance framework. If we were advising a company like the one mentioned, the priority sequence would be:
1. Establish Data Inventory and Classification: This is Step Zero. Before implementing any control, you must know what you have. A formal, mandated data inventory (including jurisdiction and sensitivity) is non-negotiable.
2. Build a Risk Framework: Once you understand what you have to protect you have to understand the risk to the business, customers and the impacts that the risk will have.
3. Adopt a Minimum Viable Compliance Framework: Do not try to achieve full certification or model compliance immediately. Instead, adopt a phased approach aligned with foundational controls, such as the core principles of NZISM or the foundational controls within the NIST CSF, ISO27001 or other national legislation. This creates an immediate, documented commitment to governance.
4. Implement "Guardrails and Pattens First": Mandate the use of Cloud Security Posture Management (CSPM) tools and automated identity access management (IAM) policies. This forces the governance structure onto the technology, rather than waiting for the technology to break the governance structure.
5. Implement "Pattens": Build the reusable structures that the organisation will reuse so the ongoing structure works within the guardrails and there are predictable testable deliverables that build with in the governance structure.
6. Build Resiliency: Having defined Risks, Governance, Guardrails and Patterns provides the foundation for business resilience it describes what could occur and then provides the manner that the business can react when there is a business impacting event. These may not cover all potential events as there are unexpected ones, they do have the underlying business impact of some form of service loss and that is what must be resolved.
7. Governance Team Buy-In: The Chief Executive Officer (CEO) must visibly mandate and resource a small group responsible solely for governance oversight, ensuring it is seen as a core business function, not an IT problem.
The Bottom Line
The risk in these emerging organisations is not that a breach will happen; the risk is that when a breach occurs, the lack of verifiable governance means they cannot prove they took reasonable care. From a regulatory or insurance standpoint, proof of process is as valuable as the security controls themselves.
About Liverton Security
At Liverton Security, we work with New Zealand and international organisations to address security risk across the full spectrum, from technology to governance to culture.
Our product suite addresses the threat vectors most commonly exploited in contemporary attacks:
- SmartGate enforces email controls at the gateway
- MailAdvisor protects against phishing, business email compromise, and malicious attachments
- WebAdvisor AI identifies AI-related risks and supports your organisation's AI adoption
- SHIFT For Outlook ensures sensitive files move safely and securely between parties
Our consulting team delivers:
- Pen testing engagements aligned to OWASP, MITRE ATT&CK, PTES, and NZISM requirements
- Security maturity assessments benchmarked against ISO/IEC 27001, NIST CSF, and the PSR
- Technical debt and vulnerability exposure reviews identifying your organisation's real attack surface
- Strategic security roadmaps that translate assessment findings into prioritised, budget-aligned remediation plans
The first step is often the most important one: understanding where you actually stand before making decisions about where to invest. Our maturity assessment process is designed to provide exactly that clarity, without the noise of vendor-driven tool recommendations or compliance theatre.
If what you have read here resonates, we welcome you to have a conversation with our team.
We can keep you cyber safe
To explore solutions and discuss your cybersecurity needs, talk to our team at Liverton Security.
Let's Chat