FILTERS EMAIL RECIPIENTS, CONTENT AND ATTACHMENTS AND ALERTS USERS WHEN A RISK IS DETECTED. PROTECT YOUR BRAND AND REPUTATION WITH MAILADVISER
KEEP YOUR EMAIL PRIVATE
Data Loss and Phishing Protection
MailAdviser is an add-in to the Microsoft Outlook email client and is designed to identify local, secure, trusted and public (untrusted) email recipients. It helps an organisation prevent emails and attachments being sent to the incorrect recipient.
- ADD-ON TO OUTLOOK ENSURES COMPATIBILITY
- INTUITIVE AND SOPHISTICATED SOFTWARE CONTROLLER
- KEY MESSAGES AND ALERTS ARE MADE VISIBLE FOR USER ACTION
KEY FEATURES
MailAdviser is a feature-rich mail controller with intuitive functionality and central control configuration.
Message Scanning
Emails can be scanned for specific keywords or patterns. This can be used to identify a variety of information such as credit card numbers or other sensitive information.
Classification
Mandatory or optional email classification ensures that malicious email address domains can be permanently deny-listed.
User Group Policy Assignment
Policies can be assigned to different users within an organisation. Based on users’ membership of either local or Active Directory groups.
Central Controller
An intuitive central controller allows the administrator to quickly and securely make changes to MailAdviser to meet business requirements.
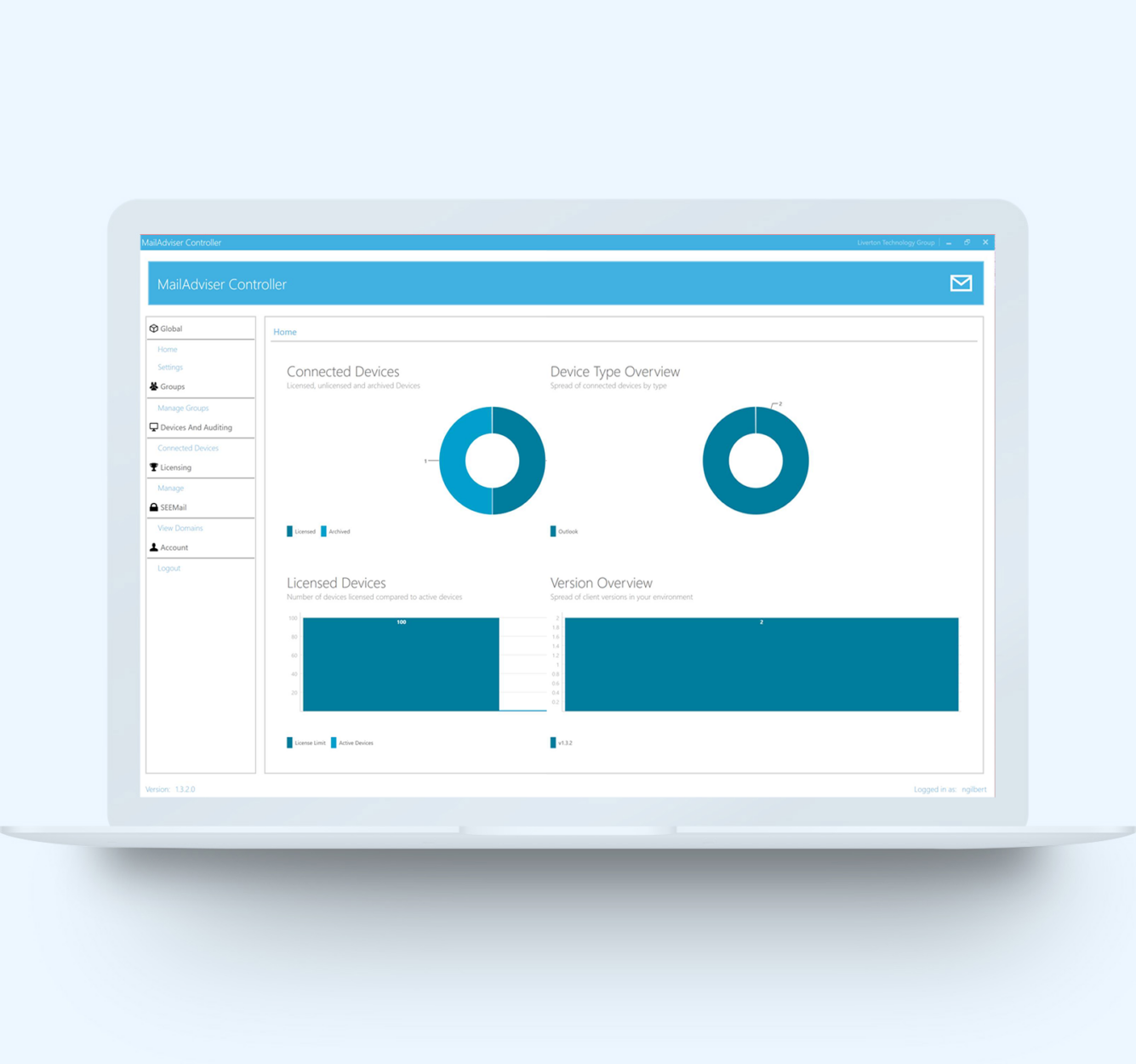
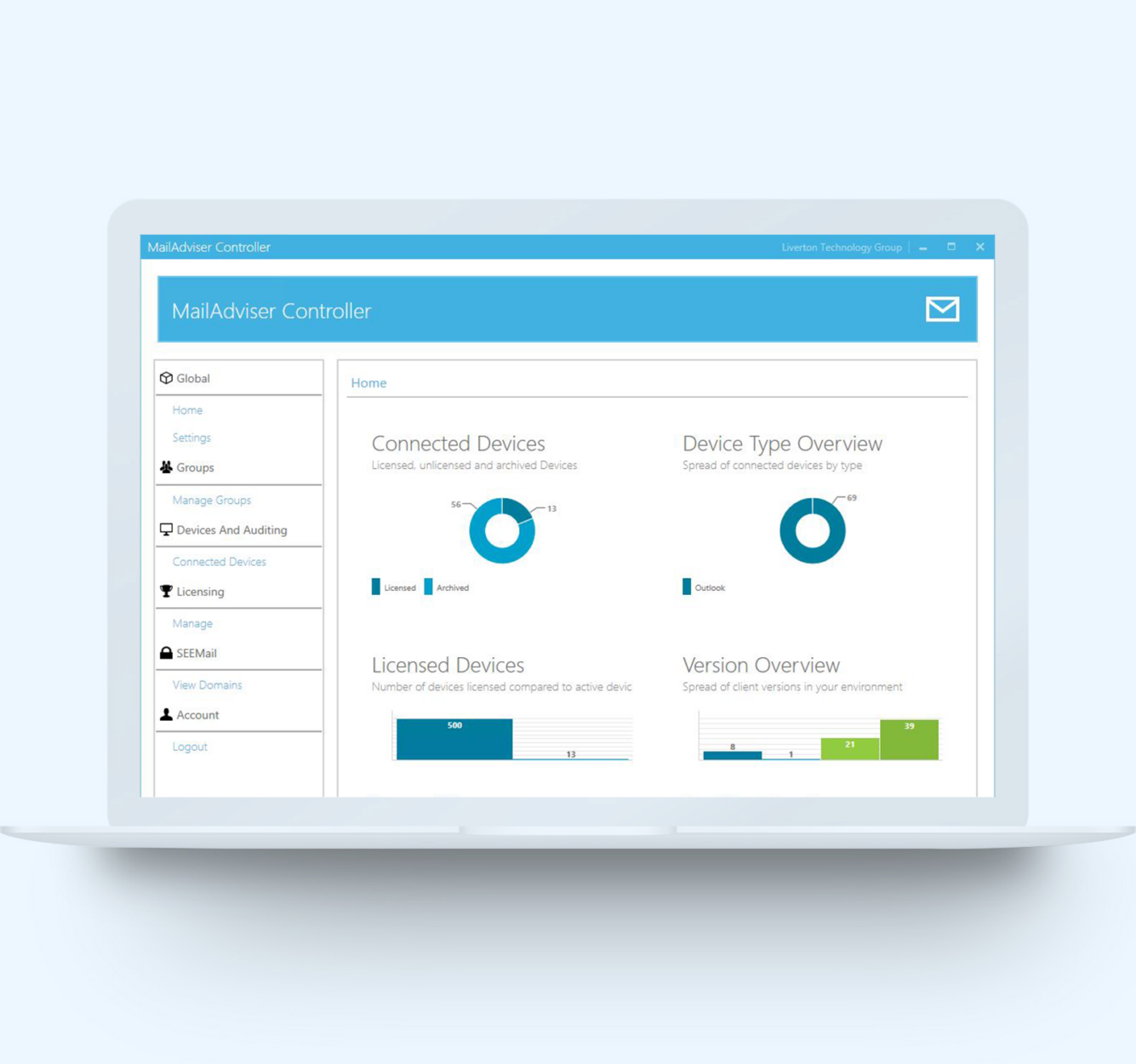
MailAdviser Central Controller
The MailAdviser Controller provides an Administrator with an intuitive user interface for managing configurations on the local MailAdviser server.
- MailAdviser will automatically retrieve Active Directory group membership every 60 minutes. Local groups can be edited at any time.
- Configure what alerts MailAdviser will display. For example warn users sending attachments larger than 25mb in size.
- Quickly manage how different devices are able to interact with MailAdviser. Access controller via mobile interface.
- Participating government and sponsored private agencies are able to use SEEMail for email identity authentication.
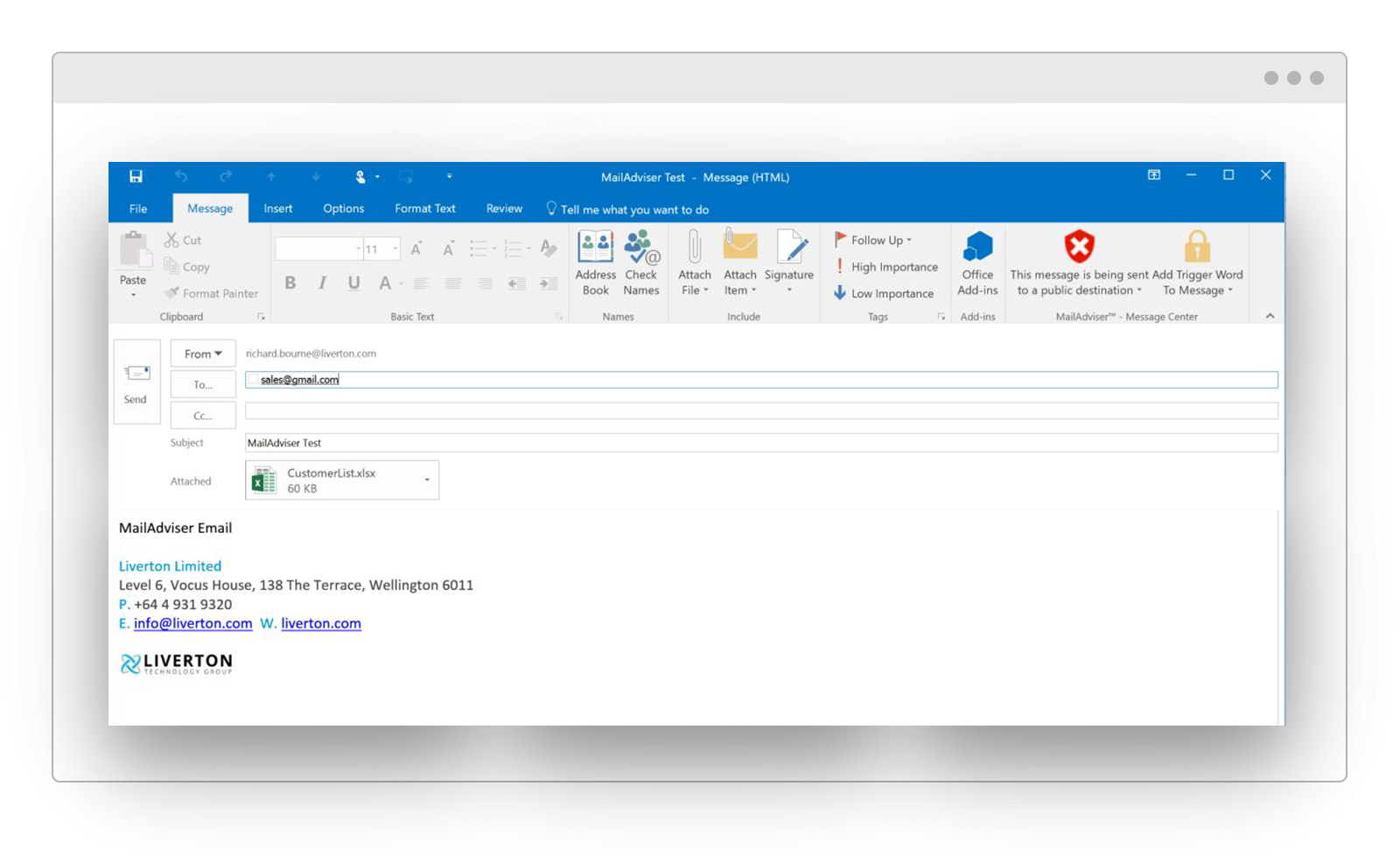
Outlook Integration
MailAdviser integrates directly into the Outlook menu ribbon. It updates the ribbon in real-time as users input email recipients.
Pop-Up Dialog
Easy to use dialog comes up whenever a threat is detected. Options to Send or Cancel message are made available to the user. MailAdviser can be configured to present the pop-up when messages are being sent to known malicious recipients.
Central Controller
IT staff are able to access a central controller to make necessary changes to the software. Central changes to the server are pushed out to client PCs when next connected.
Contact Us Today
Get in touch with our sales team to book a demo.



